Author:Wall Street CN
Recently, a craze for "raising crayfish" has swept across the internet.
Because the open-source AI agent tool OpenClaw's icon is a red lobster, it is commonly known as "Lobster." It integrates and calls communication software and a large language model to autonomously perform complex tasks such as file management, email sending and receiving, and data processing on the user's computer.
As the trend of "lobster farming" spreads, many companies have officially announced "lobster" models, and some regions have already applied them to government service scenarios.
However, there are also many risks and hidden dangers in "crayfish farming".
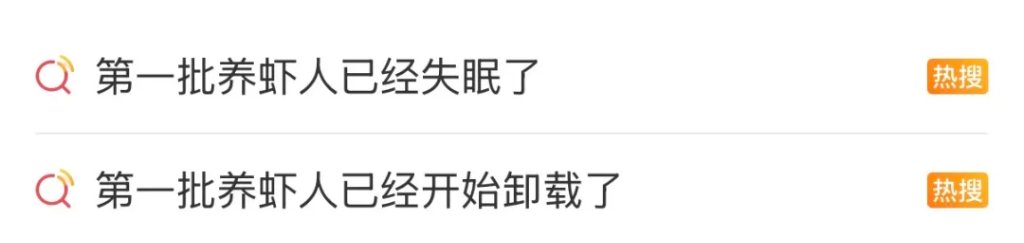
March 11,The related topic #The first batch of shrimp farmers have started uninstalling the app# has become a trending topic, sparking heated discussions among netizens.Some netizens have reported problems such as randomly deleting emails and privacy leaks during the "crayfish farming" process.
According to Cover News, a netizen shared their experience using OpenClaw online: They entrusted their work email to OpenClaw, with the instruction: "Check your inbox and list the emails you want to archive or delete." They specifically added the restriction "Do not perform any actions without permission." However, "Lobster" ignored the netizen's repeated "stop" commands and frantically deleted hundreds of emails.
According to New Consumer Daily, a programmer in Shenzhen shared that on the third day after installing OpenClaw, his API key was stolen, and he received a token bill of up to 12,000 yuan in the early morning. Because OpenClaw has extremely high automation permissions, once the key is leaked, the AI may frantically call the model in the background, causing users to unknowingly incur huge expenses.
The privacy and security risks associated with "crayfish farming" continue to raise concerns among netizens.
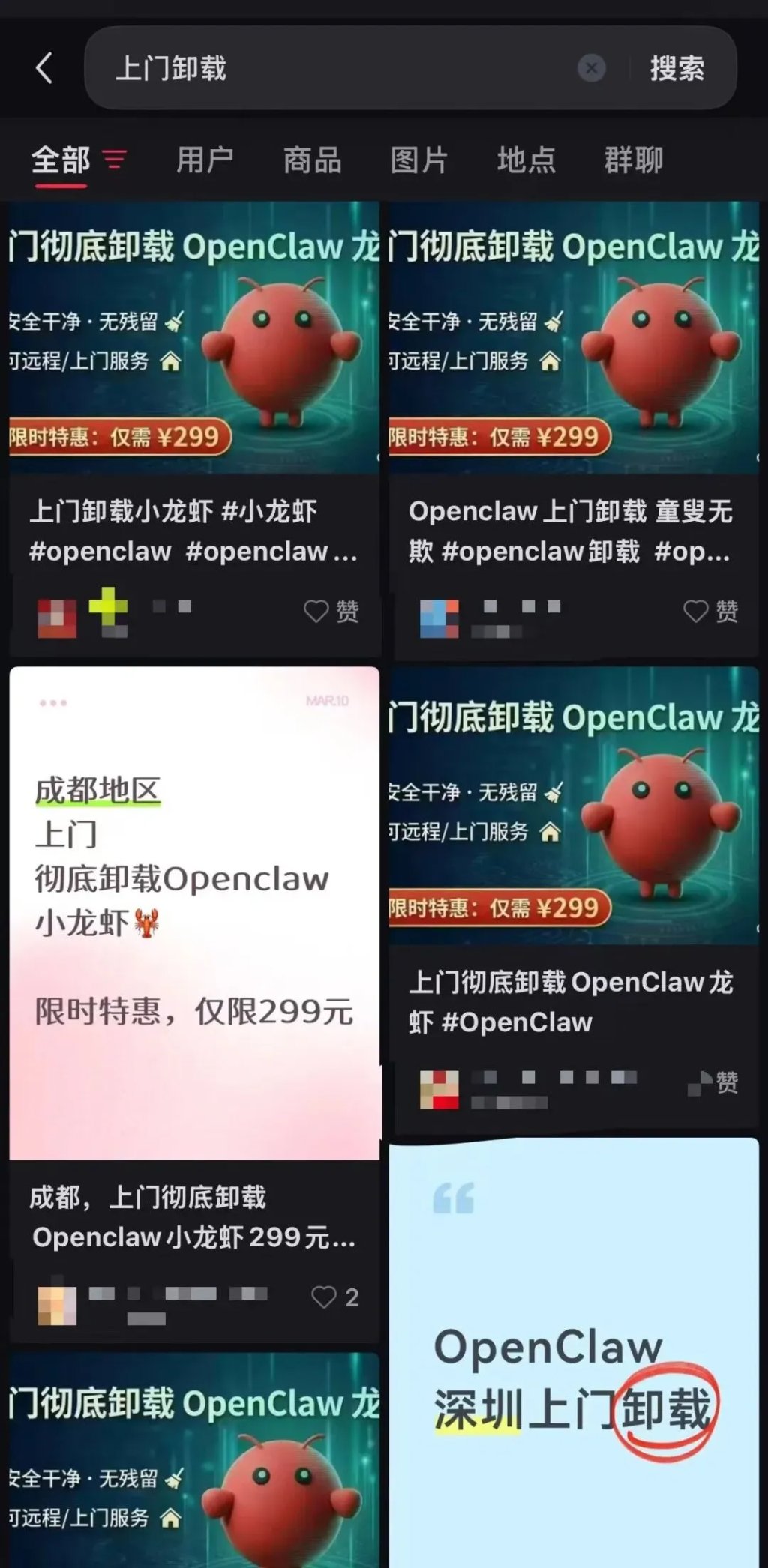
According to Blue Whale News, the explosive popularity of OpenClaw also boosted the "lobster on-site installation service" on second-hand trading platforms. However, recently, on-site uninstallation has quickly become a new hot business.
Regarding the current AI craze, some netizens believe that we should remain rational when facing emerging AI tools and avoid blindly following the trend.
Some netizens also called for the prompt enactment of relevant laws and regulations to standardize the development and use of AI technology.
Official risk warning issued
On February 5, the Cybersecurity Threat and Vulnerability Information Sharing Platform of the Ministry of Industry and Information Technology detected that some instances of the OpenClaw open-source AI agent had high security risks under default or improper configuration, which could easily lead to cyberattacks, information leaks and other security problems.
On March 10, the National Computer Network Emergency Response Technical Team/Coordination Center of China (CNCERT/CC) issued another risk warning regarding the security application of OpenClaw.
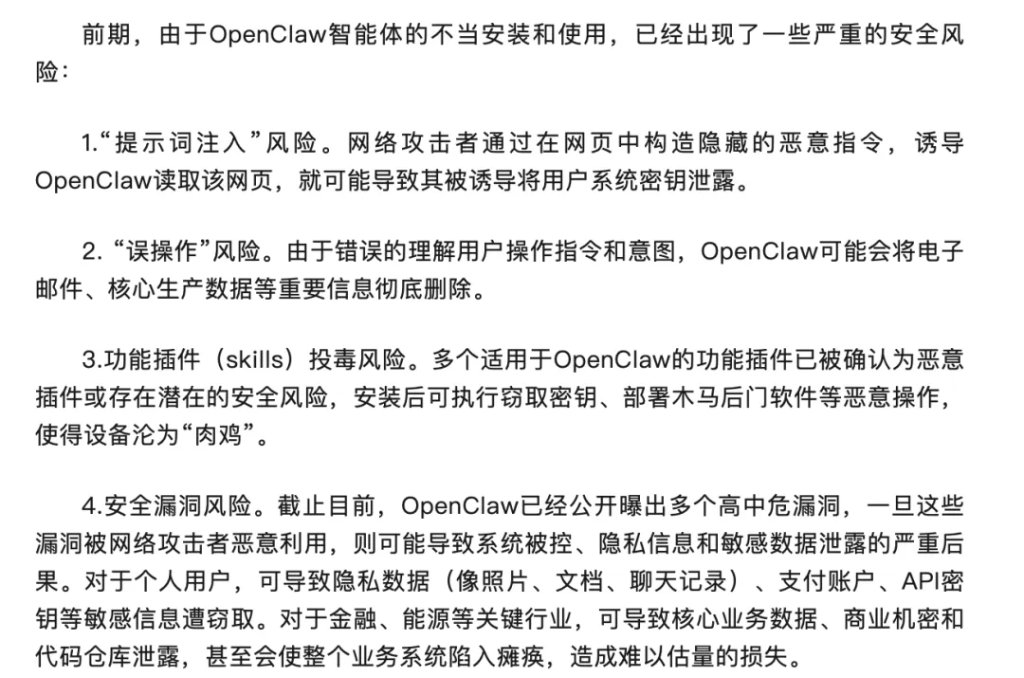
The warning states that OpenClaw's default security configuration is weak, making it vulnerable to attackers gaining complete control of the system. Currently, four serious security risks have been identified: prompt word injection, accidental operation, plugin poisoning, and security vulnerabilities.
Experts warn: Use "lobster" and other intelligent agents with caution.
Experts from the China Academy of Information and Communications Technology cautioned that although the "Lobster" AI agent has been updated to the latest version and can fix known security vulnerabilities, it does not mean that security risks have been completely eliminated.
Experts urge government agencies, enterprises, public institutions, and individual users to use "Lobster" and other intelligent agents with caution. Upon discovering security vulnerabilities in "Lobster" or other intelligent agents, or upon encountering security threats or attacks against them, they should immediately report to the Ministry of Industry and Information Technology's Cybersecurity Threat and Vulnerability Information Sharing Platform. The platform will promptly organize handling in accordance with the "Regulations on the Management of Network Product Security Vulnerabilities."
How can we safely raise lobsters?
Experts recommend the following measures for safe use of the "Lobster" AI agent:
First, use the latest official version.
When deploying, prioritize downloading the latest stable version from official channels and enable automatic update reminders. Back up your data before upgrading, and restart the service after upgrading to verify that the patches are effective. Never use third-party images or older versions.
Second, strictly control the extent of internet exposure.
Never expose the "Lobster" agent instance to the public network, and restrict access to the source address by using strong passwords or authentication methods such as certificates or hardware keys.
Third, adhere to the principle of least privilege.
During deployment, accounts with administrator privileges are strictly prohibited from being used. Only the minimum permissions necessary to complete the task should be granted. Important operations such as deleting files, sending data, and modifying system configurations should be subject to secondary confirmation or manual approval.
Fourth, use the skills market with caution.
ClawHub is a community platform that provides skill packs for users of the "Lobster" AI. These skill packs are at risk of malicious attacks. It is recommended to download them with caution and review the skill pack code before installation. Reject any skill packs that ask you to "download zip", "execute shell scripts", or "enter passwords".
Fifth, guard against social engineering attacks and browser hijacking.
Avoid browsing websites from unknown sources and avoid clicking on unfamiliar web links. It is recommended to use website filters and other extensions to block suspicious scripts, enable OpenClaw rate limiting and log auditing, and immediately disconnect the gateway and reset the password if suspicious activity is detected.
Sixth, establish a long-term protection mechanism.
Enable detailed log auditing to regularly check for and patch vulnerabilities. Government agencies, enterprises, public institutions, and individual users can combine this with real-time protection using cybersecurity tools and mainstream antivirus software. Regularly monitor risk warnings from OpenClaw's official security bulletins and vulnerability databases such as the Ministry of Industry and Information Technology's Cybersecurity Threat and Vulnerability Information Sharing Platform, and promptly address any potential security risks.
Users must thoroughly understand and implement the safety configuration specifications when using AI intelligent agents such as "Lobster" and develop safe usage habits.
This article is sourced from: